2026 Cybersecurity & Privacy Strategies for SMB Leaders: Navigating AI-Accelerated Threats, Exposure Management, and the California Delete Act
The enterprise technology and security environment has entered a phase of decisive maturity, permanently altered by the integration of artificial intelligence into the arsenals of both global defenders and highly resourced threat actors. For leaders in the small and medium-sized business (SMB) sector who span the technology, cyber, privacy, and legal domains, the events leading up to May 2026 represent a critical operational inflection point. The speed, scale, and automation of malicious cyber operations have compressed the threat lifecycle to an unprecedented degree, exposing the inherent inadequacies of reactive security paradigms and legacy vulnerability management frameworks. Concurrently, regulatory bodies across the globe, and particularly within the United States, are imposing rigorous, highly technical operational requirements on data handling, fundamentally blurring the traditional lines between IT governance, proactive cybersecurity, and legal compliance. This initial strategic briefing dissects the immediate threats observed throughout April 2026, analyzes the sweeping regulatory shifts coming into enforcement, and outlines the high-level strategic mitigations required to maintain organizational resilience.
The Problem: AI-Accelerated Exploitation and the April 2026 Breach Wave
The most profound and disruptive shift in the current cyber threat ecosystem is the radical compression of the vulnerability-to-exploit timeline. In late April 2026, the cybersecurity agency CERT-In issued a high-severity advisory directly addressing the exponential rise of AI-driven cyber threats, specifically pointing to the capabilities of advanced models and frontier AI systems. The capability of these advanced AI systems to independently analyze vast volumes of complex source code, identify zero-day vulnerabilities in widely utilized software architectures, and generate functional, weaponized exploit codes has reduced the traditional exploitation window from weeks or days to a matter of mere hours.
The automation offered by these adversarial AI models has significantly lowered the barrier to entry for cybercriminals, facilitating highly sophisticated credential theft, privilege escalation, and lateral movement across enterprise networks with minimal human intervention. Consequently, the financial and commercial sectors have observed massive spikes in fraudulent infrastructure; for instance, cybersecurity firm CloudSEK projected that fraudulent financial website domains would grow by 65% in 2026, alongside an 83% increase in fake financial applications, largely driven by AI-generated phishing content and deepfake-enabled fraud.
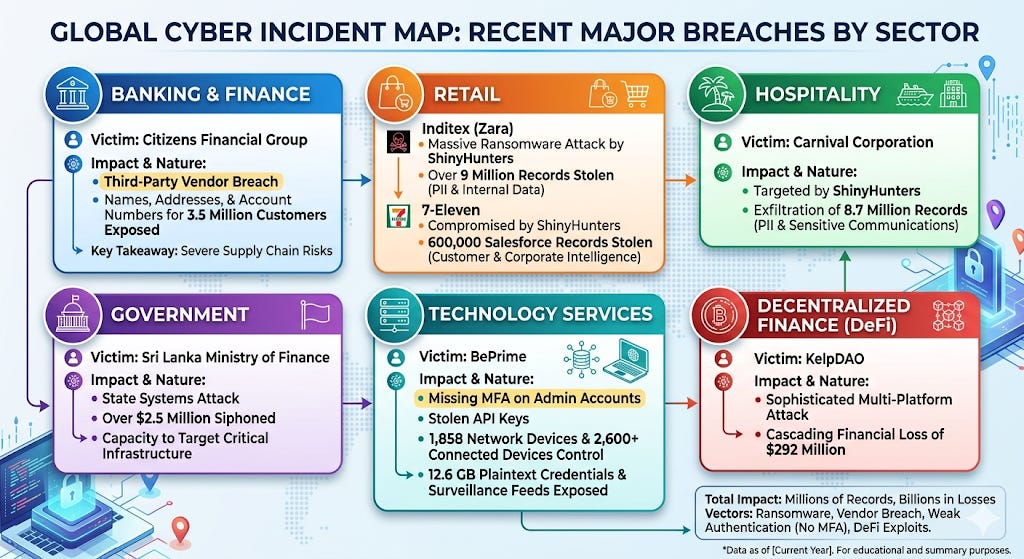
This theoretical risk of machine-speed exploitation materialized severely throughout April 2026, as the industry witnessed an unprecedented wave of massive data breaches impacting organizations of all sizes, proving that SMBs and large enterprises alike are squarely within the crosshairs of automated campaigns. The threat landscape was heavily dominated by the ShinyHunters ransomware group and other advanced persistent threat (APT) actors, demonstrating highly automated and scalable extortion tactics. The devastation observed across multiple sectors highlights the critical vulnerabilities inherent in third-party supply chains and unhardened infrastructure.
Enjoying it so far, why not subscribe to keep up on the change landscape and be prepared to defend your organization and advanced your career in the process.
Furthermore, the emergence of the "Elite Enterprise" ransomware in the wild signifies a terrifying evolution in the destructive potential of automated malware. This high-impact threat utilizes a sophisticated hybrid encryption model, combining AES-256 for rapid file encryption and RSA-4096 for asymmetric key protection, making brute-force decryption mathematically impossible. Unlike traditional ransomware, which rapidly changes file extensions and triggers immediate behavioral alarms in legacy detection systems, Elite Enterprise deliberately leaves all filenames intact post-encryption. This highly evasive tactic masks visible indicators of compromise, causing severe operational confusion for IT teams attempting to triage the incident, as users perceive spontaneous system failures or localized file corruption rather than a widespread cryptographic attack.
The malware executes a highly structured sequence of evasion and impairment tactics before revealing its presence. It systematically targets Windows backup architectures by terminating critical processes such as vssadmin.exe and wmic shadowcopy to permanently eradicate Volume Shadow Copies, denying the victim a rapid recovery path. It actively disables administrative and management tools, utilizing hidden windows and bootkit techniques to impair defenses, and subsequently disrupts MBR/VBR boot sectors. Only after the propagation and destruction phases are complete does it drop the ransom notes (elite_ransom.html and a text variant), demanding ransoms as high as 227 BTC. These notes operate with a 168-hour countdown timer and explicitly state that no communication or negotiation is possible, promising automatic decryption strictly upon payment—a psychological pressure tactic optimized for maximum, frictionless extortion.
A Case Study in Critical Urgency: CVE-2026-41940 (cPanel & WHM)
The theoretical dangers of rapid, automated exploitation were perfectly illustrated by CVE-2026-41940, a critical vulnerability disclosed in late April 2026 affecting cPanel & WHM and WP Squared platforms. Assigned a maximum CVSS score of 9.8, this vulnerability allows unauthenticated remote attackers to bypass the login flow entirely and secure root-level administrative access to the hosting control panel.
The root cause of this catastrophic flaw lies in how the cpsrvd (the cPanel service daemon) processes and writes new session files before authentication even occurs. Attackers are able to inject raw Carriage Return Line Feed (\r\n) characters via a malicious basic authorization header, manipulating the whostmgrsession cookie by omitting an expected segment and avoiding the standard encryption process applied to user-provided values. Because the system fails to properly sanitize this input before writing the session file to the disk, attackers can inject arbitrary properties directly into their session file, most notably appending the parameter user=root.
Upon triggering a reload of the session from the newly manipulated file, the attacker is instantly granted maximum administrator-level access without ever supplying a valid password. This results in the full compromise of hosted accounts, exposure of customer databases, and the ability to establish persistent backdoors for subsequent lateral movement across the hosting infrastructure. Security intelligence firms observed targeted zero-day exploitation of this specific flaw occurring in the wild as early as February 2026, months before public disclosure or patch availability, demonstrating the absolute necessity of preemptive, continuous defense structures rather than reactive patching.
The Strategic Mitigation: The Paradigm Shift to Exposure Management
The sheer volume of newly discovered vulnerabilities has rendered traditional vulnerability management (VM) programs mathematically and operationally impossible to sustain. With the National Vulnerability Database reporting over 42,000 Common Vulnerabilities and Exposures (CVEs) in 2025 alone, the strategy of indiscriminate patching is a verified failure, especially when enterprise organizations are faced with an average of 67 million security findings per year generated by disparate scanning tools.
The necessary strategic shift for SMBs and enterprise leaders alike is the transition from legacy Vulnerability Management to Continuous Threat Exposure Management (CTEM). While traditional VM focuses merely on identifying known software flaws across internal assets and prioritizing them based on generic, theoretical severity scores like CVSS, Exposure Management evaluates the actual risk based on the attacker's operational perspective. Exposure management recognizes that not every vulnerability poses a legitimate threat; an exposure only exists when a technical weakness aligns with an attacker's capabilities, is reachable within the specific network environment, and lacks sufficient mitigating controls.
To effectively mitigate the risks posed by AI-accelerated threats, organizations must ask critical, context-driven questions rather than blindly following vulnerability reports. Is this specific vulnerability reachable from the public internet? Does it reside on a business-critical asset that processes regulated data? Are there active, automated exploits currently observed in the wild?.
By focusing relentlessly on exploitability, network reachability, and business impact, Exposure Management consolidates thousands of related findings, addresses underlying root causes—such as excessive container privileges, unencrypted cloud snapshots, or identity misconfigurations—and filters out theoretical risks isolated safely behind internal firewalls. This paradigm shift allows resource-constrained SMB security teams to focus exclusively on the specific conditions that threat actors can realistically exploit. Transitioning to this model has been shown to deliver an average 40% reduction in remediation backlogs, saving organizations an estimated 33,000 hours per year and significantly reducing the operational friction between security and IT operations teams.
Actions for Improvement: Integrating Proactive Defense and Governance
To navigate the perilous convergence of AI-driven attacks, complex software vulnerabilities, and stringent regulatory compliance, organizations must adopt architectures built fundamentally on "secure by design" principles. Relying solely on human analysts to triage an overwhelming flood of alerts is no longer a viable defensive posture against machine-speed execution. Organizations must integrate automated containment, advanced identity governance, and modernized security operations centers (SOC) into their core operational fabric.
CrowdStrike Falcon is the definitive AI-native platform built to stop breaches, empowering organizations to secure their entire infrastructure at scale. This end-to-end solution unifies endpoint, cloud, and identity protection, leveraging world-class threat intelligence to keep you decisively ahead of modern, AI-powered attacks.. By implementing comprehensive, AI-native solutions like CrowdStrike Falcon, SMBs can autonomously detect behavioral anomalies, immediately isolate affected assets at the endpoint level, and effectively counter the rapid execution of modern ransomware variants before lateral movement occurs, transitioning their posture from reactive recovery to proactive prevention.
Furthermore, cybersecurity is no longer an isolated technical discipline; it has fundamentally converged with legal and privacy compliance. In 2026, privacy regulation is defined by complex, multi-layered frameworks that rigorously test the operational realities of data governance, security visibility, and executive accountability. The United States has decisively moved beyond a fragmented patchwork of loose guidelines into a mature, highly aggressive enforcement phase.
On January 1, 2026, new comprehensive state privacy laws took effect in Indiana, Kentucky, and Rhode Island, granting consumers extensive rights to access, delete, and port their data, while explicitly requiring opt-in consent for sensitive data processing. Crucially, the era of regulatory leniency is abruptly ending. The 60-day "right to cure" period for the Montana Consumer Data Privacy Act (MTCDPA) expires on April 1, 2026, meaning any violations discovered are immediately enforceable by the State Attorney General without providing the business a grace period to rectify the non-compliance.
The most operationally disruptive legislation currently altering the landscape is the California Delete Act (SB 362), which established the highly complex Data Broker Requests and Opt-out Platform (DROP). Operational as of January 2026, this centralized governmental portal allows California residents to submit a single, verified request requiring all registered data brokers to permanently delete their personal data. By the strict deadline of August 1, 2026, businesses classified as data brokers must access this platform continuously—at least every 45 days—and flawlessly honor all deletion requests across their entire digital supply chain. This legislation transforms data deletion from a simple administrative task into an intensive, highly automated, and legally perilous engineering requirement. Organizations must now urgently align their cybersecurity exposure management with their data privacy obligations, utilizing strict identity and access controls to govern data sprawl, rapidly satisfy consumer rights requests, and withstand the inevitable wave of stringent regulatory audits.
If you have enjoyed the free portion of this blog, there is even more of this great content in the premium content, so why not become a paid subscriber today?
Can you think of others who could value from this substack as well, why not share it them, share it with enough folks and you will get some free months yourself too!