2026 SMB Cybersecurity: Surviving the AI Trust Crisis
A strategic roadmap for navigating deepfakes, agentic AI risks, and the $1.5M ransomware reality.
The business environment for small and mid-sized businesses in 2026 has transitioned from a period of digital transformation into an era of digital friction, where the speed of technological adoption frequently outpaces the development of governance and security frameworks. For tech, cyber, privacy, and legal leaders, the current landscape is defined not by the novelty of individual threats but by their unprecedented scale, personalization, and automation, all driven by the democratization of advanced artificial intelligence. The following report serves as a strategic briefing for the weekly newsletter, synthesizing critical research into actionable business intelligence for the modern enterprise leader.
The Strategic Threat Landscape and Foundations of Resilience
The Weaponization of Machine Speed and the Crisis of Trust
In 2026, small and mid-sized businesses will have officially surpassed large enterprises as the primary targets for organized cybercriminal groups. This shift is not a matter of prestige but of cold mathematical efficiency. While a large enterprise may offer a higher individual payout, the explosion of attacker-friendly AI tools allows criminal syndicates to target hundreds of SMBs simultaneously with the same level of sophistication that once required a bespoke nation-state campaign. Attackers no longer strike more often; they strike smarter, utilizing automated bots that generate more than 36,000 vulnerability scans per second, a volume that accounts for more than half of all internet traffic.
The psychological core of this new threat landscape is what experts describe as a “crisis of trust”. The foundational assumption that a leader can verify an identity through a phone voice or a video call face has evaporated as generative AI enables deepfakes and voice cloning that are cheaper to produce than to detect. This erosion of trust is not merely a security concern; it is an operational bottleneck. Employees who doubt the authenticity of internal requests may hesitate, escalate unnecessarily, or follow incorrect processes, slowing down the very business speed that AI was supposed to accelerate. Business Email Compromise (BEC) has matured into Business Process Compromise, where AI-powered loops simulate entire verification workflows to authorize fraudulent financial transactions.
The Economics of Exposure: The Insolvency Gap
The financial implications of a cyber incident in 2026 have reached a critical state for the SMB market. Research identifies a widening “insolvency gap,” where the median U.S. SMB holds approximately $12,100 in cash reserves while facing an average cyber insurance claim of $264,000. This 22-to-1 ratio highlights the existential nature of even a single breach. Furthermore, approximately 40% of cyber insurance claims are now denied, with 82% of those denials stemming from an organization’s inability to verify compliance with Multi-Factor Authentication (MFA) protocols.
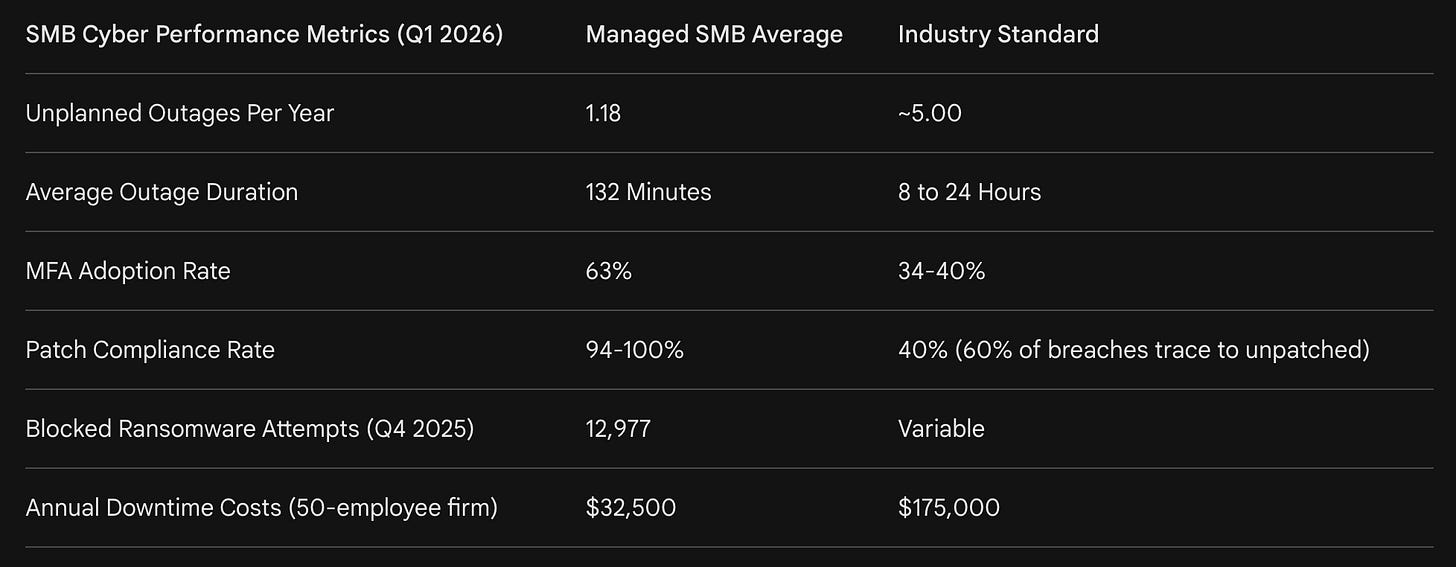
The data suggests that the cost of proactive security is significantly lower than the cost of failure. Managed clients in 2026 saw four times fewer outages and downtime costs that are 80% lower than industry averages. However, a critical recovery gap remains: only 5% of SMBs have documented Recovery Point Objective (RPO) and Recovery Time Objective (RTO) targets that have been tested within the last 90 days. This suggests that while perimeter defenses are maturing, the ability to survive a successful breach—business resilience—remains a secondary priority for many leaders.
Strategic Mitigation: Transitioning from Tools to Governance
The persistent challenge for SMBs in 2026 is “over-tooling and under-protection”. Organizations have continued to invest in security products, yet they struggle with fragmented visibility and inconsistent protection because they lack the governance to support those tools. Without clear asset inventories, defined responsibilities, and standardized practices, alerts go unaddressed and expensive technologies fail to deliver their intended value.
The shift from a reactive, checklist-driven security posture to a risk-directed approach is essential. This requires organizations to view security not as a technical hurdle, but as a core business process. In this environment, the most valuable asset an SMB can acquire is strategic expertise. Organizations that lack the internal resources to navigate these complexities often seek guidance from a dedicated security partner.
Omnistruct provides the strategic expertise needed to build and scale privacy, GRC, and security programs, empowering teams to achieve business goals without sacrificing compliance. By serving as an embedded security partner (BISO), Omnistruct delivers executive-level guidance and hands-on support to mature an organization’s security posture and align it with core business objectives.
Immediate Actions for Improvement: A 90-Day Action Plan
To close the gap between exposure and protection, leadership should focus on three primary pillars of resilience in the coming quarter: identity hygiene, process verification, and recovery readiness.
Identity Hardening: Organizations must transition critical users—including admins, finance, and executives—to phishing-resistant MFA, such as hardware tokens or passkeys. Push approvals without number matching should be disabled to prevent fatigue-based overrides.
Out-of-Band Verification: To mitigate the risk of deepfakes and AI-generated impersonation, leaders must implement mandatory waiting periods for first-time payments to new accounts and require verbal confirmation using pre-shared phrases or “trust codes” for urgent financial requests.
The 90-Day Restore Test: Beyond simply checking backup logs, organizations must perform a test restore of a critical file and time the process to validate their RTO and RPO targets. Verification of off-site backup functioning and cloud storage capacity is essential for surviving a ransomware event.
You’ve seen the "Why" behind this [Cyber/Tech Issue]—but knowing the risk is only half the battle. To move from awareness to actual protection, you need a localized execution plan.
The remainder of this deep dive is designed specifically for the SMB leader who needs to move fast without a massive enterprise budget. By upgrading to a paid subscription, you unlock:
The “How-To” Framework: A step-by-step breakdown of the [Process/Tool] mentioned above.
Resource Toolkit: Downloadable templates and checklists I use with my private coaching clients.
The Bottom Line: Direct analysis of the ROI and cost-savings associated with this strategy
Help Other Leaders Secure Their Future
The Network Effect of SMB Security
The most effective way to strengthen our SMB community is by sharing the strategies that actually work in the field. If you find value in these technical deep dives, helping a fellow leader bridge their tech gap makes the entire ecosystem more resilient. Cybersecurity is a collective effort, and more informed peers lead to a safer environment for everyone’s business.
Why Share This Subscription? When you refer a colleague to this newsletter, you are giving them access to the same specialized insights you use to lead your team:
Zero-fluff technical execution: No high-level theory, just the steps to implement.
Cost-saving vendor analysis: Honest looks at which tools are worth the SMB budget.
Direct coaching frameworks: Access to the same logic I use with private coaching clients.
Pay It Forward Use the button below to share this post or your unique referral link. When your peers join our community, we all benefit from a more secure and tech-forward marketplace.
Subscribe to Unlock the Full Strategy
Join a community of SMB leaders who stop reacting to tech shifts and start leading them.