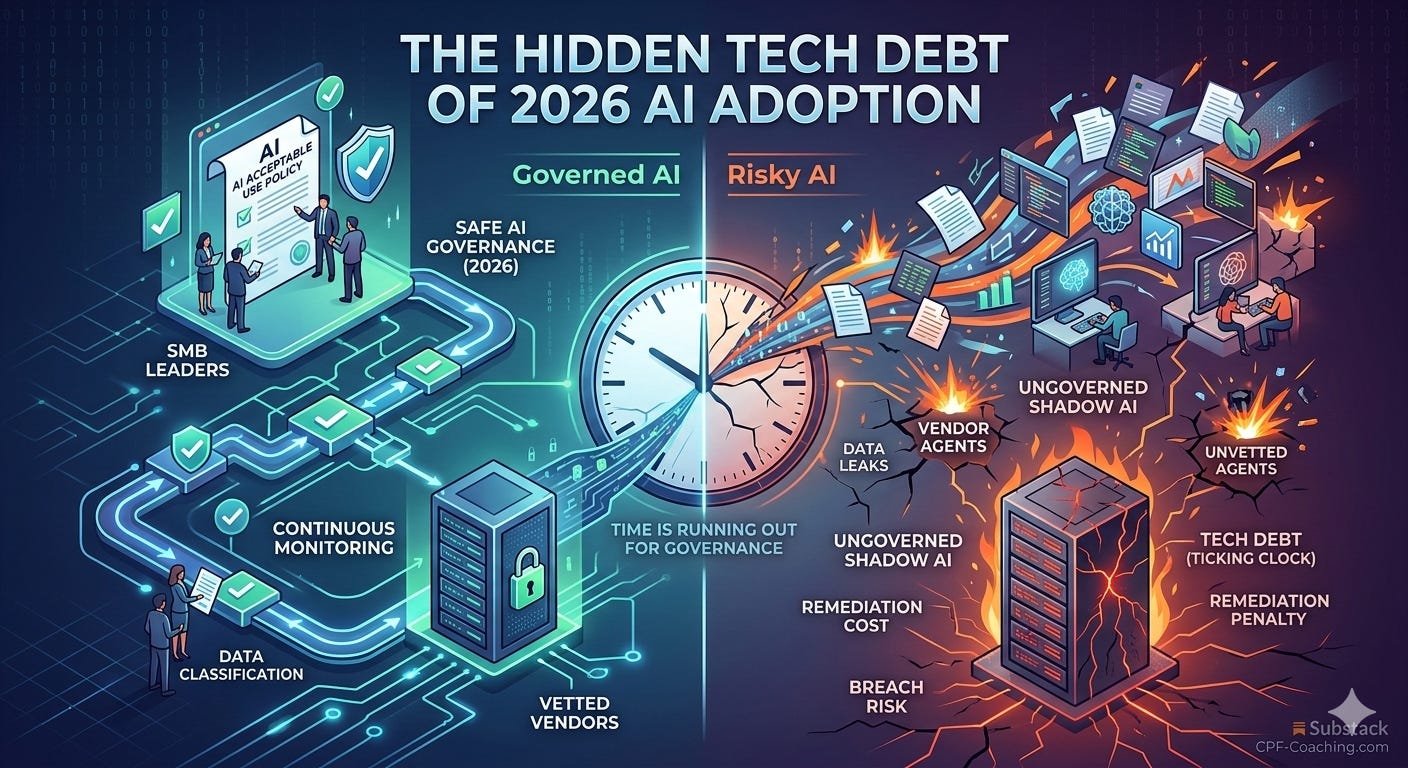
The "Hidden" Tech Debt of 2026 AI Adoption
An SMB Guide to AI Governance, Managing Third-Party Vendor Risk, and Preventing Identity-Based Attacks.
Unchecked AI experimentation is creating a new class of "Shadow Tech Debt" that will cause major security breaches and prolonged downtime in 2026 unless leaders centralize governance now.
While AI tools promised a productivity revolution, many SMBs inadvertently built a house of cards. The speed of adoption outpaced the implementation of necessary guardrails. If you do not have a formal policy for which AI tools can touch company data, you are essentially leaving your front door unlocked. The cybersecurity events of this past week prove this is no longer a theoretical risk.
I. AI-driven data leaks are the new "Shadow IT" crisis.
Employees frequently feed sensitive client information and proprietary code into free or unvetted AI tools to save time. Without formal oversight, these tools often use that data for training.
Just this week, reports surfaced detailing how a misconfigured AI application exposed over 1.5 million private records and API keys. Industry analysis surrounding this event highlighted that 63% of organizations currently lack formal AI governance policies. Relying on manual annual audits is an obsolete strategy when a single shadow AI tool can compromise millions of records overnight. You need a continuous monitoring process to ensure new integrations do not learn from your private customer data without consent.
II. The "AI Speed Tax" is crippling incident recovery.
The cost of remediation far outweighs the cost of early governance. The financial hit from an AI-related data breach is higher than traditional breaches due to the complexity of identifying exactly what data was ingested by a model.
A new Fastly Global Security Research Report released this week puts hard numbers behind this reality. The report reveals that AI-first businesses are taking an average of 80 days longer to recover from cybersecurity incidents compared to businesses that have not heavily integrated AI. This 80-day penalty stems directly from decentralized data flows and agentic workflows expanding the attack surface faster than security teams can modernize their defenses.
III. Traditional Identity Security is failing against AI-enabled threats.
As AI integrates deeper into operations, securing the identity of the user accessing those tools becomes paramount. However, relying on standard MFA is no longer enough to protect your stack.
This week, a global coalition of law enforcement disrupted Tycoon 2FA, an industrialized phishing-as-a-service platform. This platform specifically automated Adversary-in-the-Middle (AiTM) attacks to capture one-time passcodes and session cookies at scale.
Cybercriminals are buying off-the-shelf software to defeat the exact MFA tools most SMBs rely on. Moving to phishing-resistant authentication is now a baseline survival requirement for protecting your AI and SaaS environments.
If you gained value from this post, why not share it with others?
If you have not subscribed as yet, this month I will be rolling out more content for paid subscribers, to help implement the concepts we cover in your business or the ones that you support.
Below is additional content for paid subscribers to implement this weeks content.
And ask more questions