Regulatory Sovereignty: The GSA, SEC, and the "American AI" Sledgehammer
How New Procurement Mandates and Board Accountability Rules are Reshaping the SMB Leadership Playbook.
The Sovereign Identity Era: Strategic Resilience and the Fragmentation of Trust
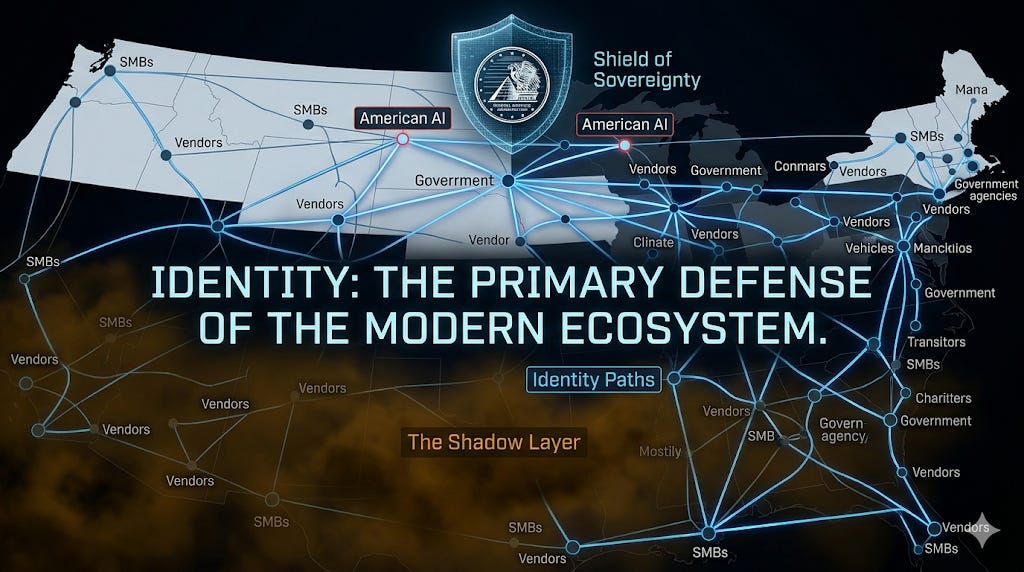
The convergence of technological autonomy and regulatory nationalism has defined the week ending March 20, 2026. For SMB leaders spanning the technical, legal, and privacy domains, the paradigm has shifted from managing discrete IT risks to navigating a complex web of “shadow layers” and “regulatory sovereignty”.
The traditional perimeter is not merely breached; it has been replaced by a fluid ecosystem where identity is the primary firewall and the supply chain is an interconnected attack surface.
The Week in Review: The Invisible Supply Chain and the “American AI” Mandate
The Epidemic of the “Shadow Layer”
The Black Kite Seventh Annual Third-Party Breach Report reveals a massive “shadow layer” of cyber victims. While 719 companies were publicly identified as victims of major breaches last year, researchers discovered an additional 26,000 organizations that were compromised but never named.
The 73-Day “Silent Window”: While intrusions are typically detected within 10 days, companies waited a median of 73 days before issuing a public notification. This delay shifts the risk onto downstream customers who remain unaware of their exposure for over two months.
Concentrated Risk: 70% of the top fifty shared tech vendors have at least one vulnerability in the CISA KEV catalog.
Stop the Breach Before the “Silent Window” Closes. 🛡️ With third-party breach notifications lagging by a median of 73 days, SMBs can no longer afford to wait for a vendor’s signal. CrowdStrike Falcon provides the AI-native, identity-first protection required to stay ahead of modern, malware-less attacks. Secure your entire infrastructure at scale and turn your identity layer into your strongest firewall. https://crowdstrike2001.partnerlinks.io/Cpf-coaching
The GSA’s “American AI” Sledgehammer
The General Services Administration (GSA) has proposed a radical contract clause, GSAR 552.239-7001, “Basic Safeguarding of Artificial Intelligence Systems” .
The Mandate: It prohibits federal contractors from using any AI components manufactured, developed, or controlled by non-U.S. entities.
The Impact: This clause takes precedence over standard commercial service agreements, forcing SMBs to verify the “provenance” of every tool in their stack.
Bodily Autonomy: Washington’s HB 2303
In a milestone for workplace privacy, Washington State has banned employers from requiring, or even requesting, that employees have microchips implanted under their skin. While marketed as a tool for streamlining office access, legislators view the ban as a necessary “preventative measure” against invasive workplace surveillance.
💡 Immediate Actionable Takeaways for SMBs
Close the “Silent Window”: Audit vendor contracts to require breach notification within 72 hours of discovery, not just determination, to bypass the 73-day industry median delay.
Inventory the AI Stack: Identify any tools in your workflow (from chatbots to coding assistants) that rely on non-U.S. components to prepare for GSA compliance.
Harden Public-Facing Apps: Exploitation of public apps rose 44% this year. Prioritize patching for the Langflow critical flaw (CVE-2026-33017) and SharePoint (CVE-2026-20963).
Lock the Front Door: Transition from SMS-based MFA to phishing-resistant passkeys or hardware tokens, as identity abuse is now the primary entry point for attackers.
More Information for subscribers below