Vulnerability Management Metrics: 15 KPIs to Measure & Mature Your Program
Measure, Monitor, and Mature Your Program with Actionable Metrics: Use data-driven KPIs to track progress, demonstrate value, and guide continuous improvement.
Last week, we continued our series on 10 Best Cloud Practices for the Modern Enterprise. This week, we will focus on measuring, monitoring, and maturing your program using actionable metrics. Utilize data-driven KPIs to track progress, demonstrate value, and guide continuous improvement.
A fundamental principle of management, often attributed to Peter Drucker, is that "you can't improve what you don't measure." This is especially true for vulnerability management. Without a robust set of metrics and Key Performance Indicators (KPIs), a security program operates in a vacuum. It becomes impossible to track progress, demonstrate value to the business, identify process bottlenecks, justify investments, or drive continuous improvement.49 A data-driven approach, built on a foundation of meaningful and actionable metrics, transforms vulnerability management from a series of disconnected activities into a measurable and optimizable business function.
Metrics serve multiple critical purposes. For technical teams, they provide operational insights into the efficiency and effectiveness of their tools and processes. For security leadership and executive management, they translate complex technical activities into the language of business risk, compliance, and return on investment. A well-designed metrics program is the engine of a mature vulnerability management lifecycle, providing the feedback loop necessary to move from a reactive posture to a proactive, continuously improving one.
Key Concepts
Tailoring Metrics to the Audience
Effective reporting requires that metrics be tailored to the audience consuming them. A single dashboard rarely serves all needs. A mature program will track and report on several categories of metrics 49:
Strategic Metrics (for Executives/Board): These are high-level metrics focused on overall risk posture, business impact, and program value. They should answer questions like, "Is our security investment reducing our risk?" and "Are we compliant with our policies?" Examples include Total Risk Remediated, SLA Compliance Rate, and overall Risk Score trends.
Tactical Metrics (for Security/IT Management): These metrics track the performance and efficiency of the vulnerability management program. They help managers answer questions like, "How quickly are we fixing critical issues?" and "Where are the bottlenecks in our process?" Examples include Mean Time to Remediate (MTTR), Average Vulnerability Age, and Number of Open Critical Vulnerabilities.
Operational Metrics (for Technical Teams): These are granular metrics that measure the effectiveness of specific tools and activities. They help analysts and engineers answer questions like, "Are our scanners covering all our assets?" and "Are our patches failing?" Examples include Scan Coverage, Vulnerability Re-Open Rate, and False Positive Rate.
Leveraging Maturity Models
In addition to tracking specific KPIs, organizations can use established frameworks to assess the overall maturity of their vulnerability management program. The SANS Vulnerability Management Maturity Model is a widely respected framework that provides a roadmap for improvement. It assesses a program's capabilities across five maturity levels (from Level 1: Initial, to Level 5: Optimized) and within five key process areas (Prepare, Identify, Analyze, Communicate, and Treat).35 Using this model, an organization can benchmark its current state, identify specific areas for improvement, and create a clear, step-by-step plan for maturing its capabilities. For example, an organization might find it is at Level 2 in "Analyze" because it still relies heavily on CVSS scores, and set a goal to reach Level 3 by incorporating threat intelligence and asset criticality into its prioritization process.85
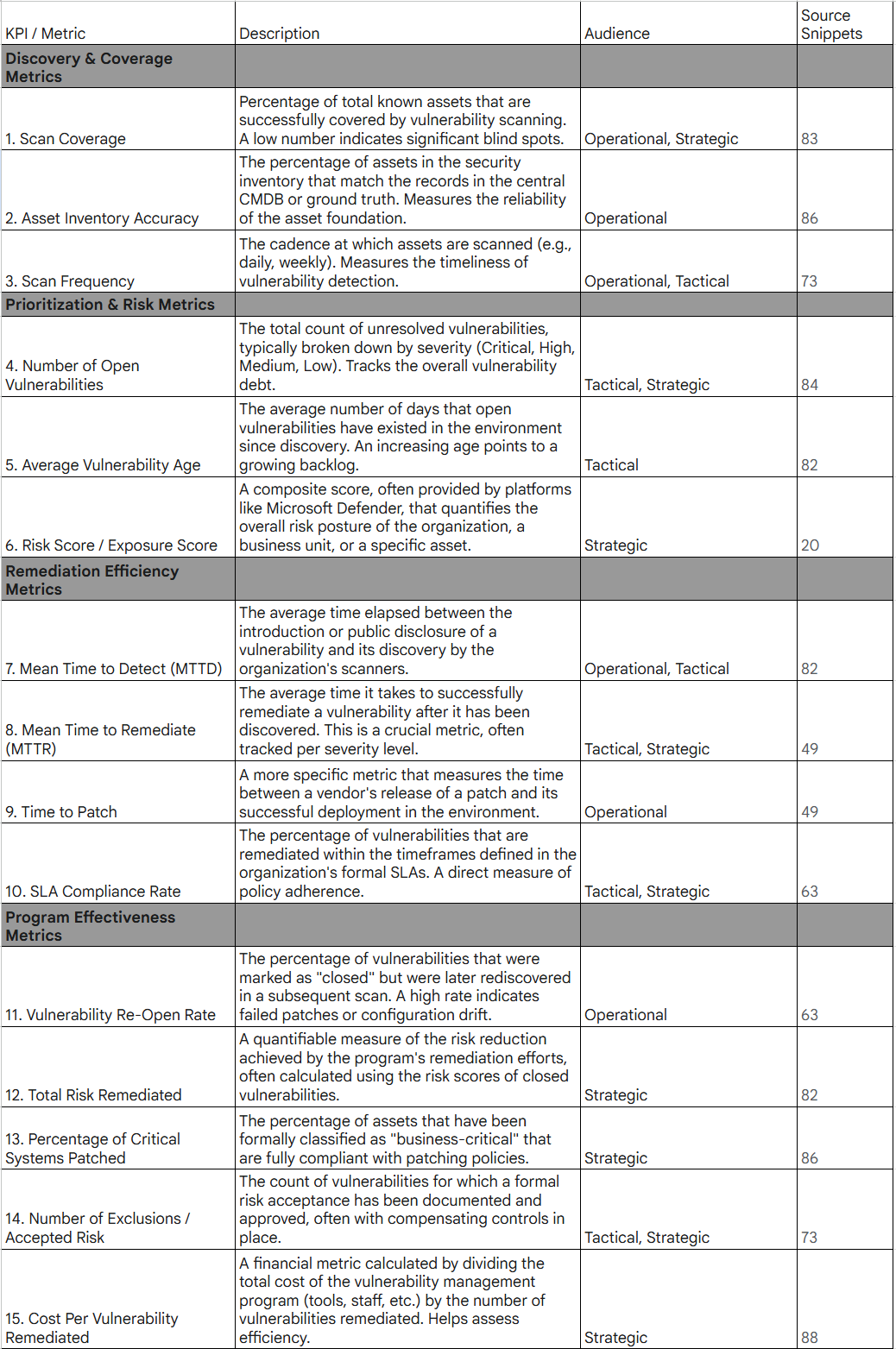
Top 15 Vulnerability Management KPIs
To implement a data-driven program, organizations should choose a balanced set of KPIs that offer visibility into all aspects of the lifecycle. The following table consolidates best practices and common metrics from various sources to provide a comprehensive starter set of 15 essential KPIs.
It is important to recognize that these metrics are not just for passive reporting; they are diagnostic tools. For example, a high MTTR is not simply a "bad number" to be reported. It is a symptom of a process bottleneck that requires investigation. It could be caused by a lack of automation, friction between the security and IT teams, or insufficient resources for testing. Similarly, a high Vulnerability Re-Open Rate signals a problem in the patch validation or configuration management process. By using these KPIs to ask "why," organizations can pinpoint weaknesses in their program and drive the targeted improvements that lead to true maturity, fulfilling the final "Improve" stage of the vulnerability management lifecycle.7
Some security tools you can consider for improving your business security posture:
CrowdStrike Falcon: An AI-driven platform for securing your infrastructure at scale and keeping up with AI advancements. https://crowdstrike2001.partnerlinks.io/Cpf-coaching
INE Security Awareness and Training is essential for your team to stay updated with the evolving threat landscape, enhancing the effectiveness of the teams supporting your organization. https://get.ine.com/cpf-coaching
Tenable helps identify weaknesses in your infrastructure, whether on-premises, in the cloud, or in your software, providing your vulnerability management with the visibility it needs. https://shop.tenable.com/cpf-coaching
Cyvatar.AI Managed endpoint protection solution for SMBs and digital cloud environment https://cyvataraif5706.referralrock.com/l/CHRISTOPHE77/
Omnistruct helps you with privacy, GRC, and security programs. They can serve as your BISO to help scale your team and security program. https://omnistruct.com/partners/influencers-meet-omnistruct/
Guidde helps you turn your tribal, undocumented processes into easy-to-follow documented videos and instructions. https://affiliate.guidde.com/cpf-coaching
Cyberupgrade simplifies the process of enhancing your cyber and digital risk management, allowing you to grow your business without having to be a compliance expert. We take care of the complexities associated with frameworks like DORA, ISO 27001, and NIS2, enabling your team to concentrate on building, scaling, and serving your customers. https://join.cyberupgrade.net/cpf-coaching
1Password secures your secrets, tokens, passwords, documents, and more, whether you're at home, work, or school. They offer programs suited for everyone. https://1password.partnerlinks.io/cpf-coaching
Work Cited:
The Vulnerability Management Lifecycle Explained (5 Steps) - PurpleSec, accessed June 26, 2025, https://purplesec.us/learn/vulnerability-management-lifecycle/
Microsoft Defender Vulnerability Management | Microsoft Security, accessed June 26, 2025, https://www.microsoft.com/en-us/security/business/threat-protection/microsoft-defender-vulnerability-management
Vulnerability Management Resources - SANS Institute, accessed June 26, 2025, https://www.sans.org/blog/vulnerability-management-resources/
Why Vulnerability Assessment Reports Fail (& How To Fix It) - PurpleSec, accessed June 26, 2025, https://purplesec.us/learn/vulnerability-assessment-reporting/
What Is Automated Vulnerability Remediation? | Benefits & Best Practices for Security Teams - Brinqa, accessed June 26, 2025, https://www.brinqa.com/blog/automated-vulnerability-remediation/
Mastering SANS Vulnerability Management: A Comprehensive Guide - Astra Security, accessed June 26, 2025, https://www.getastra.com/blog/compliance/sans/sans-vulnerability-management/
Top 10 Vulnerability Management Metrics & KPIs To Measure Success, accessed June 26, 2025, https://purplesec.us/learn/vulnerability-management-metrics/
15 Vulnerability Management Metrics to Measure your Program - Wiz, accessed June 26, 2025, https://www.wiz.io/academy/vulnerability-management-metrics
Vulnerability Management Reports | Rootshell Security, accessed June 26, 2025, https://www.rootshellsecurity.net/vulnerability-management-reports/
Using the SANS Vulnerability Management Maturity Model in Your Vulnerability Management Process - RH-ISAC, accessed June 26, 2025, https://rhisac.org/vulnerability-management/sans-maturity-model-process/
15 Key Vulnerability Management Metrics for Success - Legit Security, accessed June 26, 2025, https://www.legitsecurity.com/aspm-knowledge-base/top-vulnerability-management-metrics
Vulnerability Management Metrics: 5 Metrics to Start Measuring in ..., accessed June 26, 2025, https://www.sans.org/blog/5-metrics-start-measuring-vulnerability-management-program/
Automated Remediation: Benefits, Best Practices & Use Cases - Tamnoon, accessed June 26, 2025, https://tamnoon.io/blog/automated-cloud-remediation-guide/